The Turbulent Timeline of Cybersecurity | Vibepedia
The history of cybersecurity is a story of cat and mouse, with hackers and security experts engaging in a perpetual game of one-upmanship. The first computer…
Contents
- 🔒 Introduction to Cybersecurity
- 📊 The Early Days of Cybersecurity
- 🚨 The Rise of Malware and Viruses
- 🔍 The Emergence of Cyber Threat Intelligence
- 👥 The Role of Artificial Intelligence in Cybersecurity
- 🚫 The Evolution of Cyber Attacks and Threats
- 🤝 The Importance of Cybersecurity Collaboration and Information Sharing
- 📈 The Future of Cybersecurity: Trends and Predictions
- 📊 The Economic Impact of Cybersecurity
- 👮 The Role of Governments in Cybersecurity
- 🚀 The Intersection of Cybersecurity and Emerging Technologies
- Frequently Asked Questions
- Related Topics
Overview
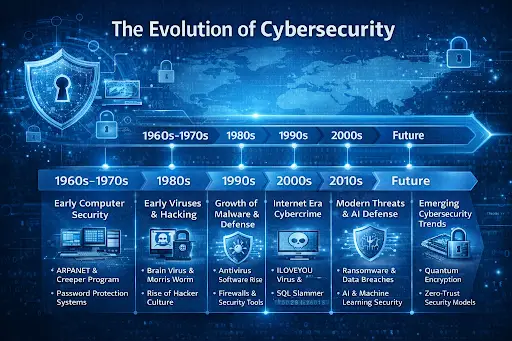
The history of cybersecurity is a story of cat and mouse, with hackers and security experts engaging in a perpetual game of one-upmanship. The first computer virus, the Creeper System, was discovered in 1971, but it wasn't until the 1980s that cybersecurity began to take shape as a distinct field. The introduction of the internet to the general public in the 1990s created new vulnerabilities, and the 2000s saw the rise of malware, phishing, and other types of cyber threats. Today, cybersecurity is a multibillion-dollar industry, with companies like Symantec, McAfee, and Kaspersky leading the charge. Despite these efforts, cyber threats continue to evolve, with the likes of ransomware, AI-powered attacks, and nation-state sponsored hacking operations posing significant challenges. As the world becomes increasingly dependent on digital technologies, the importance of cybersecurity will only continue to grow, with the global cybersecurity market projected to reach $300 billion by 2024, according to a report by MarketsandMarkets.
🔒 Introduction to Cybersecurity
The field of cybersecurity has undergone significant transformations over the years, driven by the increasing sophistication of Cyber Attacks and the growing importance of Data Protection. As we explore the turbulent timeline of cybersecurity, it becomes clear that the industry has been shaped by a complex interplay of technological advancements, Threat Intelligence, and Incident Response strategies. The History of Cybersecurity is marked by notable events, such as the discovery of the First Computer Virus and the development of the First Firewall. Today, cybersecurity is a critical component of National Security and Business Continuity.
📊 The Early Days of Cybersecurity
The early days of cybersecurity were marked by a lack of awareness and understanding of the potential threats. However, with the advent of the Internet and the widespread adoption of Computer Networks, the need for Network Security became increasingly apparent. The development of Encryption technologies and Firewalls helped to mitigate some of the risks, but the emergence of Malware and Viruses posed new challenges. The Morris Worm, discovered in 1988, is often cited as one of the first Computer Worms. As the Internet of Things (IoT) continues to grow, the need for IoT Security has become a pressing concern.
🚨 The Rise of Malware and Viruses
The rise of Malware and Viruses in the 1990s and early 2000s marked a significant turning point in the history of cybersecurity. The I Love You Virus, also known as the Love Bug, is a notable example of the devastating impact of a well-crafted Malware attack. The development of Antivirus Software and Intrusion Detection Systems helped to combat these threats, but the Cyber Threat Landscape continued to evolve. The emergence of Advanced Persistent Threats (APTs) and Zero-Day Exploits has further complicated the cybersecurity landscape. As we look to the future, it is essential to consider the role of Artificial Intelligence in AI-Powered Cyber Attacks.
🔍 The Emergence of Cyber Threat Intelligence
The emergence of Cyber Threat Intelligence has been a game-changer in the field of cybersecurity. By analyzing Threat Data and Incident Response strategies, organizations can better understand the Cyber Threat Landscape and develop more effective Security Controls. The use of Machine Learning and Data Analytics has enabled the development of more sophisticated Threat Detection systems. However, the Cybersecurity Skills Gap remains a significant challenge, with many organizations struggling to find qualified Cybersecurity Professionals. The importance of Cybersecurity Awareness and Cybersecurity Training cannot be overstated.
👥 The Role of Artificial Intelligence in Cybersecurity
The role of Artificial Intelligence in cybersecurity is a topic of ongoing debate. While AI has the potential to revolutionize the field of cybersecurity, it also poses significant risks. The use of AI-Powered Cyber Attacks has become increasingly common, with many attackers leveraging AI to develop more sophisticated Malware and Phishing campaigns. However, AI can also be used to improve Threat Detection and Incident Response strategies. The development of AI-Powered Security Tools has enabled organizations to better analyze Threat Data and develop more effective Security Controls. As we look to the future, it is essential to consider the potential benefits and risks of AI in Cybersecurity.
🚫 The Evolution of Cyber Attacks and Threats
The evolution of Cyber Attacks and Cyber Threats has been rapid and relentless. From Denial of Service (DoS) attacks to Ransomware and Zero-Day Exploits, the Cyber Threat Landscape is constantly changing. The use of Social Engineering tactics has become increasingly common, with many attackers leveraging Phishing and Spear Phishing campaigns to gain access to sensitive Data. The importance of Cybersecurity Collaboration and Information Sharing cannot be overstated, as organizations work together to combat the growing threat of Cyber Attacks.
🤝 The Importance of Cybersecurity Collaboration and Information Sharing
The importance of Cybersecurity Collaboration and Information Sharing cannot be overstated. By working together, organizations can share Threat Intelligence and develop more effective Security Controls. The use of Bug Bounty Programs and Vulnerability Disclosure policies has enabled organizations to identify and remediate Vulnerabilities more effectively. However, the Cybersecurity Skills Gap remains a significant challenge, with many organizations struggling to find qualified Cybersecurity Professionals. The development of Cybersecurity Frameworks and Compliance Standards has helped to improve Cybersecurity Posture, but more work needs to be done to address the growing threat of Cyber Attacks.
📈 The Future of Cybersecurity: Trends and Predictions
The future of cybersecurity is uncertain, but one thing is clear: the Cyber Threat Landscape will continue to evolve. The use of Emerging Technologies such as Blockchain, Cloud Computing, and Internet of Things (IoT) will create new opportunities and challenges for cybersecurity professionals. The development of Quantum Computing has the potential to revolutionize the field of cybersecurity, but it also poses significant risks. As we look to the future, it is essential to consider the potential benefits and risks of Emerging Technologies and develop strategies to mitigate the growing threat of Cyber Attacks.
📊 The Economic Impact of Cybersecurity
The economic impact of cybersecurity is significant, with the global Cybersecurity Market projected to reach $300 billion by 2025. The cost of Cyber Attacks can be devastating, with many organizations facing significant financial losses and reputational damage. The use of Cyber Insurance has become increasingly common, but the Cybersecurity Skills Gap remains a significant challenge. The development of Cybersecurity Frameworks and Compliance Standards has helped to improve Cybersecurity Posture, but more work needs to be done to address the growing threat of Cyber Attacks.
👮 The Role of Governments in Cybersecurity
The role of governments in cybersecurity is complex and multifaceted. The development of Cybersecurity Policies and Regulations has helped to improve Cybersecurity Posture, but the Cybersecurity Skills Gap remains a significant challenge. The use of Bug Bounty Programs and Vulnerability Disclosure policies has enabled organizations to identify and remediate Vulnerabilities more effectively. However, the Cyber Threat Landscape is constantly changing, and governments must work to stay ahead of the threat. The development of National Cybersecurity Strategies has helped to improve Cybersecurity Posture, but more work needs to be done to address the growing threat of Cyber Attacks.
🚀 The Intersection of Cybersecurity and Emerging Technologies
The intersection of cybersecurity and emerging technologies is a topic of ongoing debate. The use of Emerging Technologies such as Blockchain, Cloud Computing, and Internet of Things (IoT) will create new opportunities and challenges for cybersecurity professionals. The development of Quantum Computing has the potential to revolutionize the field of cybersecurity, but it also poses significant risks. As we look to the future, it is essential to consider the potential benefits and risks of Emerging Technologies and develop strategies to mitigate the growing threat of Cyber Attacks.
Key Facts
- Year
- 1971
- Origin
- United States
- Category
- Technology
- Type
- Concept
Frequently Asked Questions
What is the most significant threat to cybersecurity today?
The most significant threat to cybersecurity today is the growing sophistication of Cyber Attacks and the increasing use of AI-Powered Cyber Attacks. The Cyber Threat Landscape is constantly changing, and organizations must work to stay ahead of the threat. The use of Emerging Technologies such as Blockchain, Cloud Computing, and Internet of Things (IoT) will create new opportunities and challenges for cybersecurity professionals.
How can organizations improve their cybersecurity posture?
Organizations can improve their cybersecurity posture by developing and implementing effective Security Controls, such as Firewalls, Intrusion Detection Systems, and Encryption. The use of Bug Bounty Programs and Vulnerability Disclosure policies can also help to identify and remediate Vulnerabilities more effectively. Additionally, organizations should prioritize Cybersecurity Awareness and Cybersecurity Training to ensure that employees are equipped to handle the growing threat of Cyber Attacks.
What is the role of artificial intelligence in cybersecurity?
The role of Artificial Intelligence in cybersecurity is complex and multifaceted. AI can be used to improve Threat Detection and Incident Response strategies, but it also poses significant risks. The use of AI-Powered Cyber Attacks has become increasingly common, and organizations must work to stay ahead of the threat. The development of AI-Powered Security Tools has enabled organizations to better analyze Threat Data and develop more effective Security Controls.
How can individuals protect themselves from cyber attacks?
Individuals can protect themselves from Cyber Attacks by prioritizing Cybersecurity Awareness and taking steps to secure their personal Data. This includes using Strong Passwords, enabling Two-Factor Authentication, and keeping Software and Operating Systems up to date. Additionally, individuals should be cautious when clicking on links or opening attachments from unknown sources, and should prioritize Cybersecurity Training to stay ahead of the threat.
What is the economic impact of cybersecurity?
The economic impact of cybersecurity is significant, with the global Cybersecurity Market projected to reach $300 billion by 2025. The cost of Cyber Attacks can be devastating, with many organizations facing significant financial losses and reputational damage. The use of Cyber Insurance has become increasingly common, but the Cybersecurity Skills Gap remains a significant challenge. The development of Cybersecurity Frameworks and Compliance Standards has helped to improve Cybersecurity Posture, but more work needs to be done to address the growing threat of Cyber Attacks.
How can organizations measure the effectiveness of their cybersecurity controls?
Organizations can measure the effectiveness of their Security Controls by tracking Key Performance Indicators (KPIs) such as Incident Response times, Detection Rates, and False Positive Rates. The use of Security Information and Event Management (SIEM) systems can also help to identify and remediate Vulnerabilities more effectively. Additionally, organizations should prioritize Cybersecurity Awareness and Cybersecurity Training to ensure that employees are equipped to handle the growing threat of Cyber Attacks.
What is the role of governments in cybersecurity?
The role of governments in cybersecurity is complex and multifaceted. The development of Cybersecurity Policies and Regulations has helped to improve Cybersecurity Posture, but the Cybersecurity Skills Gap remains a significant challenge. The use of Bug Bounty Programs and Vulnerability Disclosure policies has enabled organizations to identify and remediate Vulnerabilities more effectively. Additionally, governments should prioritize Cybersecurity Awareness and Cybersecurity Training to ensure that employees are equipped to handle the growing threat of Cyber Attacks.